Criminals that steal as well as encrypt data believe they have a better chance of being paid a ransom, says CFC Underwriting
A key trend in cyber crime for 2020 is for criminals to steal as well as encrypt data to ensure that organisations or individuals are more likely to pay demanded ransoms.
Speaking at CFC Underwriting’s first cyber workshop of 2020 yesterday, Tom Bennett, cyber security incident responder at CFC, said: “I think we can already say that there’s a new trend for the year.
”The Travelex hack; that was a Sodinokibi hack and the hackers have been saying that they have stolen the data of the company Travelex, in addition to encrypting it as an extra way of incentivising payment.”
Bennett went on to explain how this type of malware originated with a software called MegaCortex – this found that only a third of its victims paid the demanded ransoms, therefore it designed a model where data was both stolen and encrypted; this has infiltrated the hacker marketplace.
Bennett added: “10 of the most common [hackers], all of them are stealing data in addition to encrypting it, so it’s making it more problematic to avoid paying.”
Hacking is also becoming big business; Bennett noted that many hacking organisations now operate as a franchise, complete with customer service departments that ensure data has been decrypted once a ransom has been paid.
For example, organisations that develop ransomware or malware to sell on to other hackers often receive a 10% cut from any ransoms paid.
The highest ransom that CFC Underwriting has seen amounted to $1.2m.
Bennett said that the average ransom demanded is usually around $70,000, while the highest ransom he has heard of in London totalled $16m.
Although the transaction of paying ransoms is not illegal, once the money is in the hackers’ hands, it becomes illegal and businesses may be investigated by the police.
The exception to the rule is sanctioned entities, such as government agencies – it is illegal to pay ransoms to sanctioned entities and individuals could face up to 10 years in prison for doing this.
Remote desktop abuse
According to Bennett, another common type of cyber crime that affected many businesses last year was brute force attacks on remote desktop servers. This is where hackers obtain an organisation’s IP address, and then guess low security administrator passwords, such as Password1. This accounted for 63% of ransomware attacks last year.
Other types of ransomware attacks used last year, according to CFC’s data, include phishing (17%) and remote desktop abuse where credentials are stolen (17%).
Business impacts
Also speaking at the cyber workshop was Will Hodson, cyber analyst, and Lindsey Nelson, UK and international cyber team leader.
Hodson discussed business interruption insurance, highlighting the main differences between a cyber incident and a more physical incident, such as if a fire occurs at an organisation’s manufacturing plant. The key difference is that cyber incidents affect intangible assets, versus tangible assets that may be destroyed in a fire.
This could include, for example, an insurer buying search engine optimisation (SEO) services if a data breach has led to an insured’s website dropping down Google’s rankings, therefore attracting less customers.
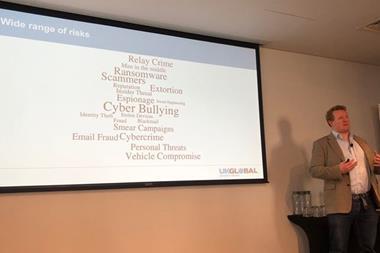
Linked to this, Nelson spoke about the reputational harm that can follow a cyber-attack – she described this type of cover as the “next level” of business interruption insurance. Some policies, she said, only cover PR and media costs rather than full reputational harm.
CFC writes £100m gross written premium (GWP) for standalone cyber policies, out of £500m total GWP - £20m of this £100m figure is in the UK market. CFC further stated that it dealt with around 2,000 cyber incidents in 2019.














![acquisition three jigsaw]](https://d17mj6xr9uykrr.cloudfront.net/Pictures/274x183/4/9/8/122498_acquisitionthreejigsaw_905211.jpg)







































No comments yet