The Insurance Times editorial team brings you all the latest updates from the Cyber Insights event held in London, as they happen.

17.17 Insurance Times events editor Martin Kornacki is delivering his closing remarks, bringing to an end a very thought-provoking day of discussion.
17.15 After a breach it is important to be clear about who needs to know what about what happened – customers in particular.
16.57 Kenny Henderson, special counsel at law firm Covington & Burling, has taken to the stage to give three case studies about cyber attack responses
16.42 96% of recent cyber attacks could have been defended against
16.40 Cyber crime has become a business. It is now more organised.
16.38 The average cost of a breach is £2.5m
16.37 Customer data is being lost so frequently that customers have started to suffer from ‘notification fatigue’
16.36 A cyber attack can be one of the most costly and damaging incidents a company can face
16.34 Vijay Rathour,vice-president of risk management firm Stroz Friedberg has taken to the stage to talk about incident response in cyber attacks.
16.26 Standardisation of cyber exposure data is necessary for the development of a proper cyber insurance market – Simon Ruffle
16.23 Such an outage could result in an insurance claims bill of $21.4bn for the insurance industry if it ran for two weeks but up to $71.1bn if it ran for four weeks.
16.21 Business interruption insurance cover typically does not kick in until after 7, 14 or 21 days of disruption, so such a power outage would need to run for a long time to trigger policies.
16.20 Simon Ruffle is discussing what would happen if a cyber attack on power generators cut power to 93 million people in the US
16.08 Simon Ruffle, director of technology research and innovation at the Cambridge Centre for Risk Studies, has taken to the stage to discuss stress testing companies’ cyber exposures.
16.00 “Disgruntled IT employees are the most dangerous employees you have.” – Brendan Saunders
15.57 Phishing is not limited to the classic badly-worded emails inviting you to disclose your personal bank account details. They can be more sophisticated. One study by NCC found that 70% of a company’s employees could not distinguish a phishing site from their company’s own site.
15.56 A lot of the large-scale hacks have been caused by targeted social engineering – encouraging people to click on links from phishing emails
15.53 Third parties need to be considered: a company’s network does not stop at the perimeter of the network that it owns and controls
15.51 Outdated component versions in custom applications, network segregation and physical network entry points are also key vulnerabilities for companies.
15.49 Applications developed in-house are another threat for companies
15.48 Over-reliance on anti-virus software is also a key risk. It should be a last line of defence, and reliance on it is a bad idea.
15.47 Out-of-date, unpatched software is one of the key vulnerabilities for corporations
15.41 Brendan Saunders at the NCC Group has just taken to the stage for the discussion on best practice for managing and mitigating key cyber risks.
15.15 Some companies are now seeing cyber security as a competitive advantage, and chief executives are starting to see that good cyber security can win market share.
15.13 If a company you are insuring doesn’t have dynamic threat monitoring, your risk assessment is only as good as the day you first did it, and no better – Robert Hayes.
15.10 Companies often suffer a new attack within 90 days of the first because the hacker found a number of ways in and only used one.
15.09 Companies need a communications strategy for when a breach occurs.
15.07 If a company has not got dynamic threat monitoring, it is not going to be secure, no matter how good its firewall or access restrictions
15.01 Cyber risk management is not just about technology, it is also about policy. For example, how long does it take to remove someone’s IT privileges after they are fired from a company?
14.59 If companies cannot implement security patches to systems within four to five days, they are vulnerable to attacks
14.51 Organisations in every sector fail on almost all key security criteria.
14.49 Just-in-time authentication can prevent a breach turning into a company-wide disaster.
14.46 Robert Hayes, senior director of the global cyber security and data protection group at Microsoft, has taken to the stage to talk about best practice for managing cyber risks.
14.42 Most breaches are caused by a simple mistake. The TalkTalk hack was very straightforward.
14.41 Ken Munro: “Your people can be fantastic security ambassadors. Teach them about security.”
14.35 A hacker could use access to a WIFI-connected kettle to bypass security features and cause a fire. What kind of claim would this be? Ken Munro says: “There are so many claims implications for the internet of things. It is going to be fascinating over the next few years.”
14.31 Ken Munro has just demonstrated how to find out someone’s WIFI key from their WIFI-connected kettle.This could ultimately allow a hacker to access bank details. He said: “The internet of things is about turning back the clock in terms of security. It’s a train wreck.”
14.26 Voice control is a key vulnerability in smartphones and other devices.
14.21 Bring your own device is “bring your own security disaster” – Ken Munro
14.19 Using a password manager, which generates a long, complicated password, can help alleviate the problem of re-used password.
14.17 First-party cyber liability insurance cover is “absolutely essential” in the UK – Ken Munro.
14.15 Disabling macros in Microsoft Office documents can help prevent hacks.
14.11 It’s not difficult for a company to get to a reasonable level of security. The vulnerability is through customers.
14.08 If company B gets hacked because of passwords stolen from company A, where company A’s customers reused their passwords, whose fault is it?
14.05 The game changer about the recent TalkTalk hack was the fact that they went public about it.
14.04 The majority of breaches we see are there because of mandatory breach disclosure, says Ken Munro

14.02 Ken Munro, partner at Pen Test Partners has taken to the stage for a live demonstration of a hack
13.03 Bamford has called the new EU regulation which is currently in the trialogue phase a game changer.
He adds: “It will include increased mandatory reporting, more enforcement and greater regulatory powers. It will also bring the greater possibility of class actions.”
13.01 Cyber liability insurance should incentivise people to do the right thing - Bamford
12.54 Bamford says: “It is important that we pay attention to the fact we are heading in the direction of increased breach notification enforcement. It is not heading the other way.
”The direction of regulation is also for more Independent supervisory organisations like the ICO to undertake regulatory audits. We will be seeing more compensation being awarded by the courts.”
12.48 Bamford says the regulation has grown as the risks have grown. But the laws have not kept pace with the risk to incentivise people to take measures against that risk.
This led to the ICO office being given the powers to fine for serious breaches of data protection laws.
12.44 Information Commissioner’s Office (ICO) head of strategic liaison Jonathan Bamford is now on stage to talk about current regulatory developments.
12.42 In conclusion, Hiscox’s Webb believes cyber will continue on standalone policies, Calderbank agrees but adds that it will include bolt-ons, while Hogg and Camillo agree that there should be more specialisation.
12.39 Calderbank adds: “From an underwriting perspective, Cyber Essentials is a starting point. As a business you need to be aware that the insurance is the final piece in the puzzle. You need to have everything in place and on top of that you need to look at the culture. It is not just what they do but the way they look at the risks. We are also looking for companies that are continually updating their culture and procedures.”
12.36 Liberty’s Hogg says the programme is too stringent.
“For us it is about a risk culture towards information security – not just in the IT, but across HR, training.”
12.32 Martin Kornacki asks the panel their view on the government Cyber Essentials programme.
12.26 Liberty’s Hogg says: “Industry will have to work together with new vendors and expertise to create less siloed products.”
12.20 Another poll: Do you think property manage should remain a cyber exclusion? 70% say yes while 29% say no.
12.13 HCC’s Calderbank says: “I would suggest at the SME level that brokers focus on two or three markets.”
He adds that brokers should know their products. At the larger end, the larger brokers need to know all insurers in the market.
12.10 Liberty’s Matthew Hogg says it is much harder for a broker to get into the complexities and appreciate the difference between a good and bad policy unless they make it their day to day business and this does not just apply to smaller firms.
12.08 Hiscox’s Webb says: “Keeping it simple is critical and you want to give someone in an organisation a comprehensive level of cover, but the challenge you have is that it is a free market, with many competitors bringing in different things into scope.”
Webb adds that it presents a challenge to brokers because there are different limits and definitions.
12.05 Are insurers doing enough to explain their cyber-products to you clearly? 38% say only in some cases, 58% say no, while 4% say yes.
12.01 HCC’s Simon Calderbank says: The increase in enquiries we are seeing are at the smaller end. A lot of brokers are asking about what they can get. It is definitely on the increase from awareness and regulation point of view.
12.00 Hiscox’s Webb says: “We have received more enquiries in the first three months of this year than in the whole of last year.”
12.00 The panel are also asked the same question.
11.58 Poll: Have you experienced an increased number of enquiries about cyber coverage following recent high profile cyber breaches. 81% say yes, while 19% say no.
11.56 Now time for the insurers’ panel to talk about exploring cyber insurance products, pricing and risk modelling.
On the panel are: AIG EMEA head of cyber Mark Camillo, Hiscox cyber and data underwriting head of technology Matthew Webb, Liberty Specialty Markets, underwriting manager strategic assets Matthew Hogg and HCC senior technology and cyber underwriter Simon Calderbank.
11.50 “You need a good PR company that understands breaches. Customers have short memories but shareholders may not.”
11.49 “Small breaches can be expensive, particularly when you are dealing with multiple jurisdictions,” Cole says.
11.48 Cole is giving an example of a business that was stopped from trading for four months by the regulator as a result of a breach.
11.40 What should companies do to prepare?
Cole says organisations still have a lot of paper documents. She gives an example of a business that moved premises and left paper documents with sensitive customer data behind.
Cole adds: “Understand what data you control, own or possess. Understand how the legislation will impact your business. You need to demonstrate to the regulator that you understand how you get customer consent.
“In the event of a breach companies need to know the data which has been breached, number of impacted individuals, shareholder response and risk of breach leaked to press.”
“Engage privacy lawyers so you know what the requirements are to notify individuals, businesses and regulators.”
11.38 The implications of data breaches include: increased notification, wider scope, increased rights of individuals, increased enforcement, fines and penalties
11.34 Beazley UK and International breach response manager and claims manager Sandra Cole is talking about exploring the legal requirements and real-life implications of data breaches.
11.30 Cloud security is inherently weak so businesses need to have a look at that. You should also not transmit information ‘in the clear’. Methods such as tokenisation and encryption should be used.
11.29 Companies also need to do background checks on people within their firms and they also need to do checks on their portable media such as laptops, i-phones, i-pads. These can all have proprietary data.
11.29 There are strategies that people need to put into practice to protect themselves. You need to ask yourself who has access to your data, otherwise only restrict access to those that need to know.
11.27 In the event of a data breach you also have the costs associated with improving your defences. You will also need to install some sort of call centre to deal with the surge of enquiries.
11.27 We have seen many examples in the US being fined in excess of $1m by their regulators. It is not quite to that level here just yet but there is legislation being spoken about in European Union where a business could be fined up to 2% of your turnover.
11.26 In the event of a data breach you are going to have your staff spending a significant amount of time reassuring customers who have and have not been affected.
11.25 Milner says: “In the event of a data breach social media will be all over you like a cheap suit.
11.21 Milner says: “The single largest risk is loss of reputation, but regrettably insurers have been slow to providing cover for loss of reputation. There is the loss of revenue and there are also costs associated with resurrecting your image.”
11.19 Miller Insurance Partner Simon Milner is up on stage to talk about the key risk exposures associated with data breaches and measures to protect against them.
10.45 Newman talks about the potential cost of the TalkTalk breach. Following a hack, legal advice could cost around £150,000. Forensic investigation could cost around £250,000. Notifying four million people you have lost their data - £4m, Crisis communications - £100,000, Call Centre operations - £500,000, Business interruption – £25m.
10.30 Newman adds that gangs use social media to find out information about companies.
10.26 Newman says: “There is a huge obsession with privacy breaches when it comes to cyber, but the reality in the UK is a bit different. For a UK PLC this is not the only thing businesses should be worried about. The most common form of malware is CryptoLocker. CryptoLocker is mass market and untargeted.”
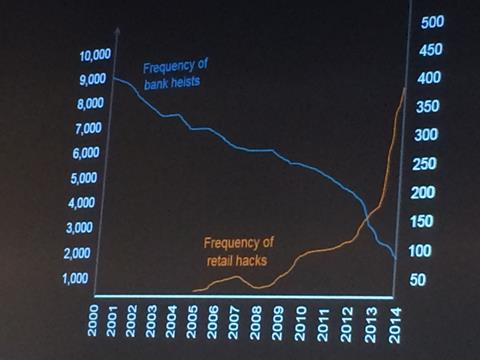
10.21 “Cyber crime has become the new form of crime,” Newman says. ”Traditional crimes have fallen by 70% over the past 15 years. Cyber is now a bigger issue than traditional crimes. UK businesses are exposed globally you do not have to be in the same country to commit cyber-crime. That is the key thing about cyber-crime. It is now a lot more lucrative than any other crime and the chances of getting caught are pretty slim.”
10.20 Newman says the Heartland Hack of 2010 by Albert Gonzalez brought with it a new era of cyber-crime.
10.18 Newman: “We are currently living through the technological revolution, but maybe what we don’t talk enough about is how it has transformed the world of crime. We are facing a different criminal to that of the types of Ronnie Biggs in the 60s.

10.16 CFC Underwriting chief innovation officer Graeme Newman is now speaking about what key cyber-crimes means in practice for the UK market.
10.13 Paragon’s Wright says: “Some of these products do exists at the moment, but I am not sure there are a great number of carriers offering that
10.10 Hodson says: “We are moving in that direction. At the top end people still buy multi-line policies and they buy cyber as standalone. But where insurers offer package policies, we are seeing package bolt-ons. That dovetailing under a single brand is beginning to happen
10.08 Question from the floor: “It would make it a lot easier if brokers like me could get different products better aligned.”
10.06 Tony Knight says that customers do not know a lot about cyber but adds that it has created a ‘whole new breed’ of consultants.
10.02 Wright says businesses also need to be aware they can have a loss without also having an event
09.58 Hodson talks about the growth in vishing scams that he is seeing.
09.56 Marsh’s Wares says from a business interruption point of view businesses are very scared about that as well as the hacking element as well.
09.52 Time for another poll: How many of your clients understand cyber risk? 12% say none of my clients, 76% say a minority of clients, 12% say the majority of my clients,
09.46 “There isn’t a great deal one can do other than understanding your clients’ exposure. It’s essentially about what is not covered,” Paragon’s William Wright.
09.43 Knightsure’s Knight says: “We try not to use the word cyber, so I use the word tech more. This helps customers understand better what they are buying. Cyber brings images of cyber men and ‘Doctor Who’ and creates the ‘it will never happen to me syndrome’.”
09.40 Gallagher’s Hodson says: “I didn’t think the TalkTalk hacking would promote much interest in our clients in the UK. Now we are getting clients calling us up to say they want cyber cover but that is creating challenges in itself because they don’t know what they want.”
09.38 First poll to start off the day: Is cyber cover currently a growth area for your business - 80% say yes, 10% say not yet, but I expect this to change soon while No, and I don’t think this will change for some time.
09.36 On the panel are Arthur J Gallagher head of technology, Richard Hodson, Knightsure Insurance Brokers managing director Tony Knight, Marsh Ltd, EMEA, cyber risk practice leader, EMEA, Stephen Wares and Paragon International Insurance Brokers Ltd, senior vice president, privacy, cyber and technology, William Wright.
09.35 The Brokers’ Panel Discussion is just about to start
09.30 Chairman and Insurance Times events editor Martin Kornacki is giving his opening remarks.
Cyber Insights 2015 will begin at 0930















































No comments yet